Thank you, to all of our donors, supporters and community partners, for your support over this past year and for your commitment to helping us in our mission to end intimate partner violence and help survivors rebuild their lives. As an integral part of our donor community, you help keep our doors open for women and children escaping abuse. Together, we welcome them in into our home, and provide the hope and safety they urgently need.
In 2023, Interval House commemorated 50 years of helping women and children flee abuse and look to a brighter future. It’s only because of your support that we were able to reach this milestone and see how far we’ve come together. Thank you again for being part of this incredible community, one that spans decades and generations.
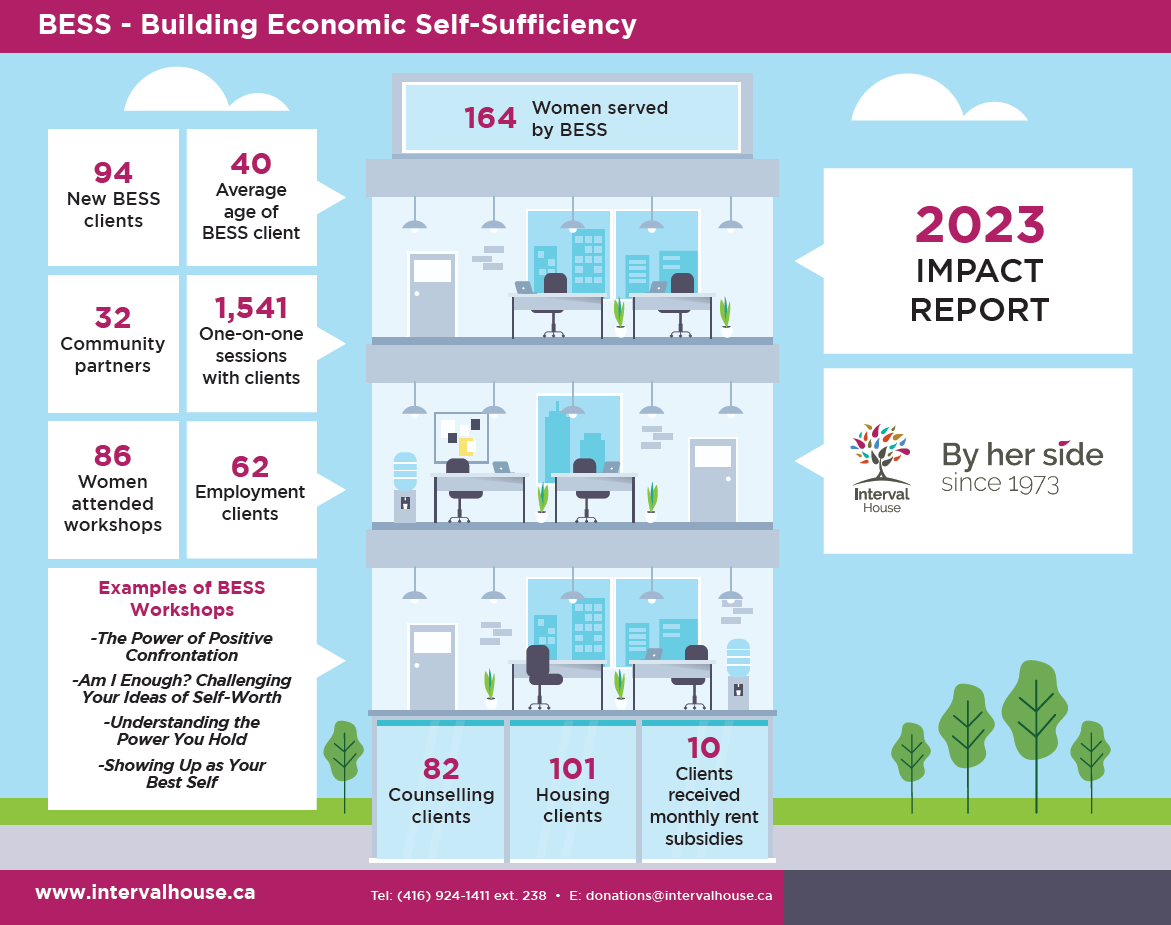
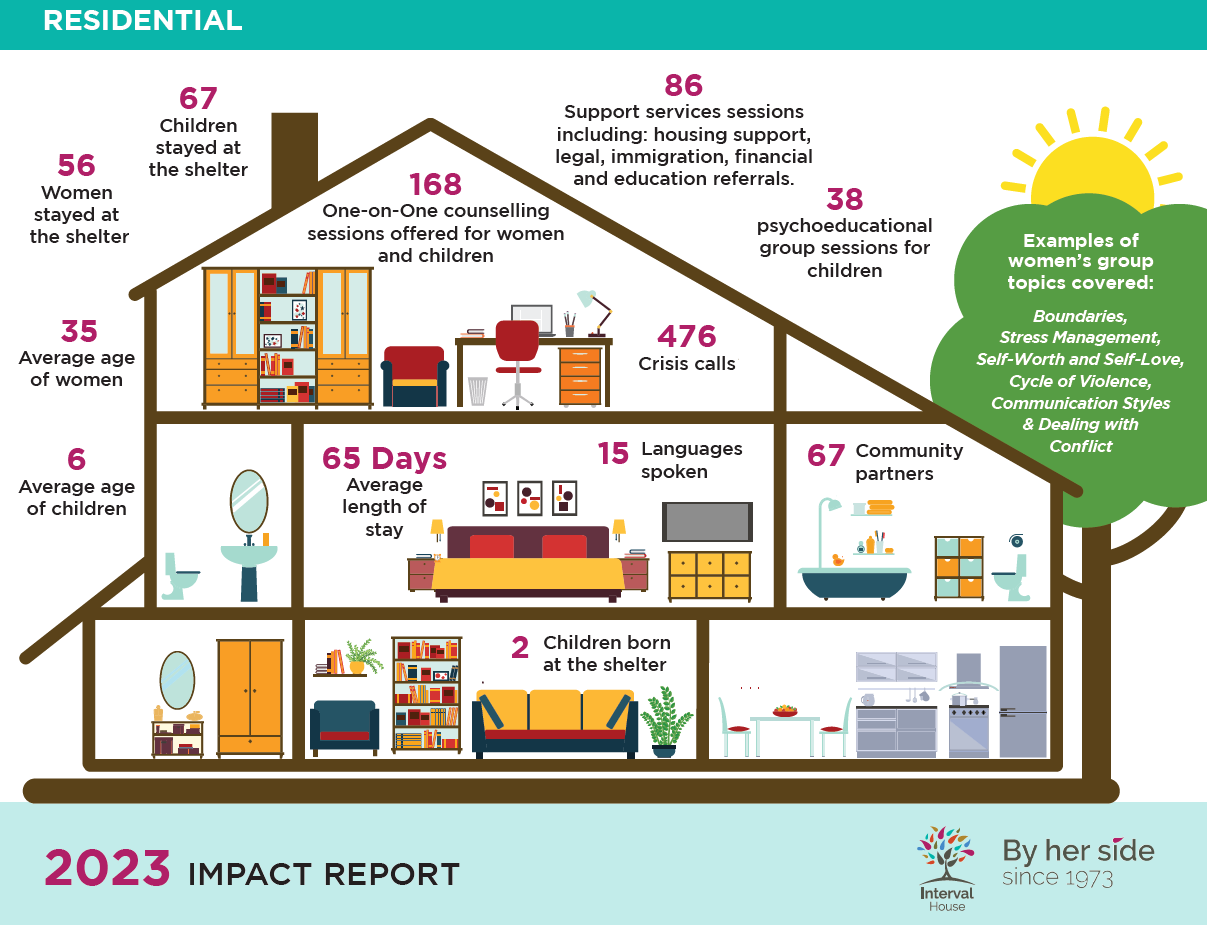
We simply couldn’t do what we do here without your leadership. We are proud to share with you the life-changing impact you have made possible in 2023.
Check out our 2023 Impact Report to see what has been happening at Interval House.
Why do you support Interval House? We’d love to hear why you choose to support Interval House and why helping women who have experienced intimate partner violence is important to you.
Please complete this quick supporter survey.
Interval House – 2023 Impact Report